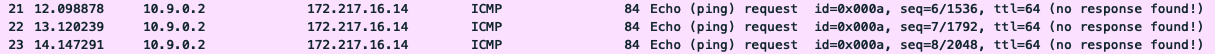
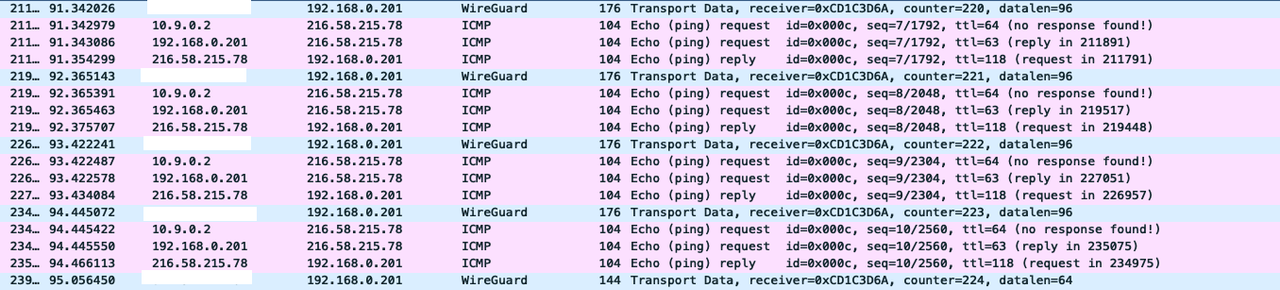
I have freshly reflashed my old buster WIreguard VPN server to bullseye and Wireguard is not working anymore. It worked well on buster though. I did some digging using tcpdump on the board and found the traffic from the wireguard client - my phone is actually forwarded to eth0 and out, but when the response gets back from the internet to eth0, it’s not forwarded back to wg0. This is kinda strange as all iptables rules are the same on my bullseye. So I can’t figure out what’s the problem here. Maybe you did encounter the same issue?
Bug report reference code: d4a5c44f-cbf9-4eb9-b34b-d564702d8e19
Device model : Odroid XU3/XU4/MC1/HC1/HC2 (armv7l)
# iptables -L -v
Chain INPUT (policy ACCEPT 0 packets, 0 bytes)
pkts bytes target prot opt in out source destination
Chain FORWARD (policy ACCEPT 0 packets, 0 bytes)
pkts bytes target prot opt in out source destination
149 8940 ACCEPT all -- wg0 any anywhere anywhere
Chain OUTPUT (policy ACCEPT 0 packets, 0 bytes)
pkts bytes target prot opt in out source destination
# iptables -L -v -t nat
Chain PREROUTING (policy ACCEPT 0 packets, 0 bytes)
pkts bytes target prot opt in out source destination
Chain INPUT (policy ACCEPT 0 packets, 0 bytes)
pkts bytes target prot opt in out source destination
Chain OUTPUT (policy ACCEPT 0 packets, 0 bytes)
pkts bytes target prot opt in out source destination
Chain POSTROUTING (policy ACCEPT 0 packets, 0 bytes)
pkts bytes target prot opt in out source destination
66 4141 MASQUERADE all -- any eth0 anywhere anywhere
# sysctl -a | grep forward
net.ipv4.conf.all.forwarding = 0
net.ipv4.conf.all.mc_forwarding = 0
net.ipv4.conf.default.forwarding = 0
net.ipv4.conf.default.mc_forwarding = 0
net.ipv4.conf.eth0.forwarding = 1
net.ipv4.conf.eth0.mc_forwarding = 0
net.ipv4.conf.lo.forwarding = 0
net.ipv4.conf.lo.mc_forwarding = 0
net.ipv4.conf.wg0.forwarding = 1
net.ipv4.conf.wg0.mc_forwarding = 0
net.ipv4.ip_forward = 0
net.ipv4.ip_forward_use_pmtu = 0
net.ipv6.conf.all.forwarding = 0
net.ipv6.conf.all.mc_forwarding = 0
net.ipv6.conf.default.forwarding = 0
net.ipv6.conf.default.mc_forwarding = 0
net.ipv6.conf.eth0.forwarding = 1
net.ipv6.conf.eth0.mc_forwarding = 0
net.ipv6.conf.lo.forwarding = 0
net.ipv6.conf.lo.mc_forwarding = 0
net.ipv6.conf.wg0.forwarding = 1
net.ipv6.conf.wg0.mc_forwarding = 0
# lsmod
Module Size Used by
binfmt_misc 20480 1
sctp_diag 16384 0
sctp 270336 5 sctp_diag
tcp_diag 16384 0
udp_diag 16384 0
inet_diag 20480 3 tcp_diag,sctp_diag,udp_diag
unix_diag 16384 0
nft_chain_nat_ipv6 16384 1
nf_conntrack_ipv6 20480 1
nf_defrag_ipv6 20480 1 nf_conntrack_ipv6
nf_nat_ipv6 16384 1 nft_chain_nat_ipv6
ip6t_MASQUERADE 16384 1
nf_nat_masquerade_ipv6 16384 1 ip6t_MASQUERADE
nf_tables_ipv6 16384 3
nft_chain_nat_ipv4 16384 1
nf_conntrack_ipv4 16384 2
nf_defrag_ipv4 16384 1 nf_conntrack_ipv4
nf_nat_ipv4 16384 1 nft_chain_nat_ipv4
ipt_MASQUERADE 16384 1
nf_nat_masquerade_ipv4 16384 1 ipt_MASQUERADE
nf_nat 24576 4 nf_nat_masquerade_ipv6,nf_nat_ipv6,nf_nat_masquerade_ipv4,nf_nat_ipv4
nf_conntrack 106496 8 nf_conntrack_ipv6,nf_conntrack_ipv4,ipt_MASQUERADE,nf_nat_masquerade_ipv6,nf_nat_ipv6,nf_nat_masquerade_ipv4,nf_nat_ipv4,nf_nat
libcrc32c 16384 3 nf_conntrack,nf_nat,sctp
nft_compat 20480 2
nft_counter 16384 4
nft_meta 16384 4
nf_tables_ipv4 16384 3
nf_tables 73728 13 nft_chain_nat_ipv6,nft_chain_nat_ipv4,nft_compat,nf_tables_ipv6,nf_tables_ipv4,nft_meta,nft_counter
nfnetlink 16384 2 nft_compat,nf_tables
wireguard 139264 0
ip6_udp_tunnel 16384 1 wireguard
udp_tunnel 16384 1 wireguard
sg 32768 0
w1_gpio 16384 0
evdev 24576 0
wire 24576 1 w1_gpio
uio_pdrv_genirq 16384 0
uio 20480 1 uio_pdrv_genirq
exynos_gpiomem 16384 0
fuse 86016 1
ip_tables 24576 0
ipv6 376832 58 nf_conntrack_ipv6,nf_nat_masquerade_ipv6,udp_diag,wireguard,nf_nat_ipv6,sctp
sd_mod 49152 0
uas 20480 0
usb_storage 49152 1 uas
scsi_mod 135168 4 sd_mod,usb_storage,uas,sg
spidev 20480 0
spi_s3c64xx 20480 0
gpio_keys 20480 0
extcon_usb_gpio 16384 0